Chances are your nonprofit handles a significant amount of personal, financial, and confidential information, making it an attractive target for cybercriminals. Without a proper cybersecurity plan in place, you risk losing valuable funding and supporters’ trust.
In this guide, we’ll explore five best practices for safeguarding your data and overcoming the challenges associated with cybersecurity:
- Create password guidelines for your staff.
- Implement software and system updates as soon as they’re available.
- Conduct regular cybersecurity training with your staff.
- Back up your files.
- Develop a cyberattack response strategy.
Whether you’re using technology to launch a digital fundraising campaign, store donor information, or manage finances, adopting these safeguards will ensure that your mission doesn’t get derailed by cybersecurity risks.
1. Create password guidelines for your staff.
Strong passwords are the first line of defense against unauthorized access to donor data, financial records, and other confidential information. Create clear guidelines such as:
- A secure password management system: A secure password management system is essential for storing passwords. Invest in a reputable tool that encrypts and stores passwords for all users, making sure that it’s only accessible to authorized personnel.
- Lengthy, unique passwords: For a password to be strong, it should have a minimum length, special characters, numbers, and mixed cases. You should also educate staff and volunteers about the importance of using unique passwords for each account and avoiding common mistakes like using personal information. Implement a password strength meter in your password management system or on login screens to provide real-time feedback to users, encouraging them to create stronger passwords.
- Two-factor authentication: Two-factor authentication adds an extra layer of security beyond just a password. It requires users to provide two different types of credentials, typically a password and a code sent to their smartphone or a hardware token, to access an account or system. This makes it significantly harder for unauthorized individuals to gain access to sensitive information.
Team members should also avoid saving passwords in case their device gets stolen or they have to change computers.
2. Implement system updates as soon as they’re available.
According to AccuData, regularly updating your system and processes should be part of your larger data hygiene procedures. Updates ensure that security vulnerabilities are patched, reducing the risk of unauthorized access, data breaches, and potential leaks of sensitive information.
Run system updates for tools like your:
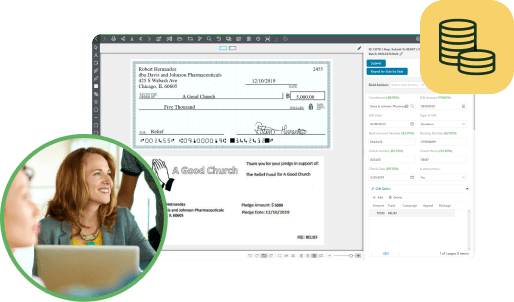
- Customer relationship management (CRM): Your nonprofit CRM contains highly sensitive donor data, including payment details, giving history, and contact information. Consider working with a technology partner to ensure your solution is secure and up to date. Doing so will minimize the risk of a data breach and protect the privacy of your supporters.
- Content management system (CMS): A CMS is the backbone of your website and its content. As such, it requires regular security fixes, bug patches, and feature enhancements. Neglecting these updates can make your website susceptible to hacking attempts and defacements.
- Accounting software: Cybercriminals frequently target financial systems to commit fraud. With AP automation tools, you can keep your accounting software protected against such threats, maintain accurate financial records, and ensure your organization’s financial stability.
- Antivirus/antimalware software: Antivirus and antimalware software detect and remove malicious software, viruses, and other threats that can compromise your organization’s systems. The software must stay current with the latest threat detection techniques to effectively protect against evolving cyber threats.
To minimize disruption, schedule these updates during periods of lower activity. For instance, it may be best to schedule them after normal business hours or on the weekends.
3. Conduct regular cybersecurity training with your staff.
Host quarterly or yearly training sessions in which you teach staff how to identify and address common cybersecurity threats like:
- Phishing: Staff should be cautious of emails, calls, and text messages from unknown sources that request sensitive information or prompt them to click on suspicious links. These messages may appear legitimate at first glance, but often include misspellings, grammatical errors, and an unusual sender address.
- Malware and ransomware: Educate staff about the risks associated with downloading files or software from untrusted sources, as this can lead to malware infections or ransomware attacks that can lock access to critical data until a ransom is paid.
- Social engineering: Attackers may pretend to be a supervisor or coworker to manipulate individuals into revealing confidential information or providing unauthorized access to systems. Employees should verify the legitimacy of these requests with a supervisor, especially when handling sensitive data.
Ensuring your staff is on the same page about cybersecurity is especially important if some or all team members work remotely. Include lessons on how team members should access your networks while working from home. For example, you might establish a policy of not connecting to your secure network when a team member is working from a public place, like a coffee shop or airport.
It’s also important to tailor your training to the specific technology that you’re using. For instance, if your nonprofit is using artificial intelligence (AI) to automate fundraising tasks, BWF recommends checking to see if the solution is transparent about its approach to data sourcing and protection.
4. Backup your files.
Backing up files ensures that critical data is protected in the event of accidental deletion, hardware failure, or cyberattack. It acts as a safety net, allowing you to recover lost data and minimize disruptions to operations.
For the best results, keep these tips in mind as you back up your files:
- Automate backups to ensure they are performed regularly and consistently without the need for manual intervention.
- Adhere to the 3-2-1 rule, which involves having at least three copies of data, stored on two different types of media, with one copy stored offsite.
- Regularly test the restoration process to check that backups are valid and can be successfully restored in case of a data loss event.
It’s also important to implement appropriate security measures when sharing files among team members. This includes restricting who has access to files, as well as monitoring file access and activity logs to detect any unusual or suspicious behavior.
5. Develop a cyberattack response strategy.
Create a plan of action to quickly respond to cybersecurity issues if they arise. This involves:
- Assigning team members to different roles. The roles and responsibilities of your cybersecurity task force will vary depending on the size and complexity of your technology. However, you should have someone in charge of data recovery and crisis communications, making sure they are well-versed in these areas.
- Taking immediate steps to mitigate damage. Disconnect from the affected networks and power down compromised accounts to prevent further fraudulent activity.
- Investigating the cause of the breach. Identify the scope of the attack, engage outside professionals as needed to help identify the source, and take steps to prevent similar issues in the future.
With a solid plan in place, you can better respond to and recover from security incidents.
By adopting these best practices, you’ll be on the right track toward protecting your nonprofit. However, it’s important to note that cybersecurity is not a one-and-done deal. Continue to evaluate and update your cybersecurity measures to stay safe against emerging threats.
Does your team have processes in place for protecting your constituent data in your CRM? Explore PairSoft’s natively integrated solutions with at-rest and in-transit data encryption by getting a demo today.